Onepoint
Contents
Introduction
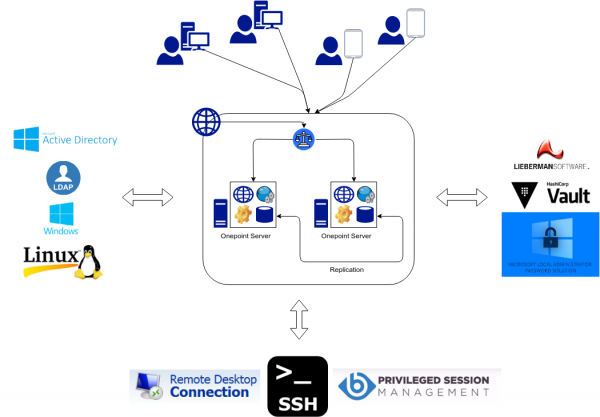
Onepoint enables Systems Integration for the IT environment. Through its disciplines concepts, it allows the integration of IT assets, modules, systems and units into a single and widelly connected among all parts, creating the possibility to creating actions, tasks and flows involving all those parts.
Installing Onepoint
You can easily follow our instructions regarding Installing Onepoint and install it. To run it, you will need a valid license, generated by our team. Any questions, send to contato@netbr.com.br.
Architecture
Onepoint components:
Backends
Backends are a Onepoint-specific concept. They are components of the computational environment designed to carry out a task or a group of related tasks for a Discipline. They allow requests and operations on the target systems through Onepoint REST calls. They also allow the integration of asynchronous tasks directly on the target systems, through Onepoint Scripts calls.
Backends Configuration
For configuration, see Backends Configuration.
Primary Backends
Primary Backends are backends that can be instanced, parameterized and extended to integrate environment's own components, such as vaults, user directories, ticketing systems, authentication systems and authorizations systems.
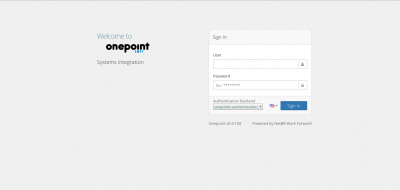
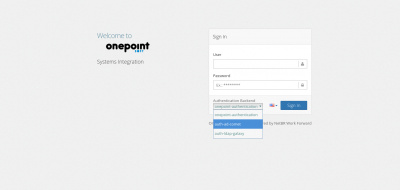
Authentication Backends
Responsible for user identity authentication. After a positive response from 'login' operation, Onepoint generates a session for operating the system. It's an extensible backend. In other words, it's possible to integrate other authenticators into onepoint, including supporting Multi-Factor Authentication and Single Sign-On tools.
Directory Backends
Responsible for managing directory data (user, groups and membership). It's a extensible backend type, allowing integration of external directories.
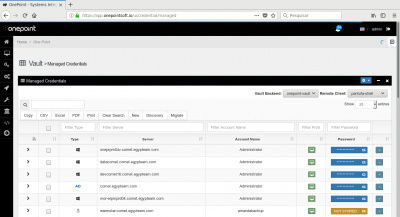
Vault Backends
Responsible for the storage, management and integration of credentials, passwords and secrets. It's an extensible backend, what allows the integration of third-party vault systems.
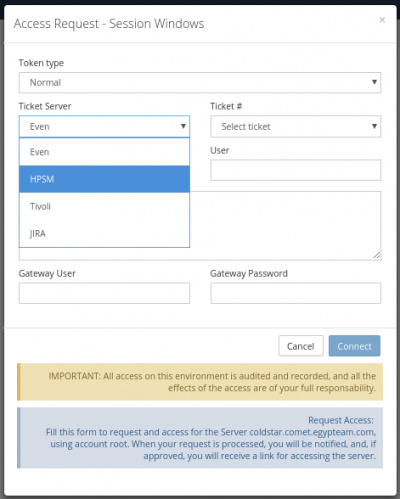
Access Session Backend
Responsible for the channels and protocols for access establishment, such as RDP and SSH. It's an extensible backend and can support other protocols.
Secondary Backends
Secondary Backends are internal and/or fixed backends, that can't be instanced, parameterized or extended.
Access Backend
Responsible for the management of access tickets and authorization based on rules for the request. It's not an extensible backend.
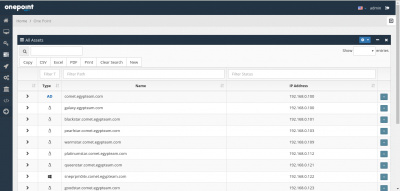
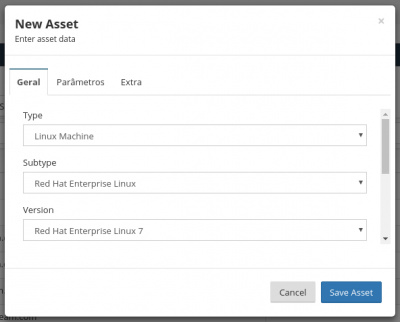
Asset Backend
Responsible for the records of managed systems. It's not extensible.
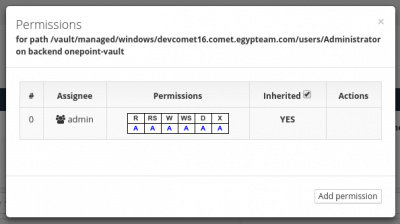
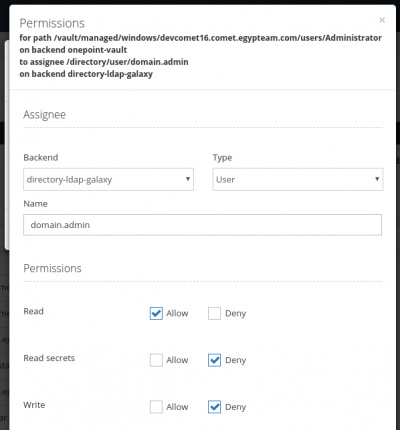
Authorization Backend
Responsible for verification of permissions on the requested resource(s) for the logged in identity. It's not an extensible backend. It works with permissioning based on Access Control Lists, Groups and Inheritance support
Backend Backends
Responsible for serving and managing backends. It's not an extensible backend.
Flow Backend
Responsible for managing and operating 'workflows'.
Policy Backend
Responsible by managing and maintening resources' policies features. They can be:
- Synchronization Policies - Interbackend data synchronization
- Cache Policies - Assigning a backend as cache of another backend
- Expiration Policies - Rules for objects expiration
- Migration Policies - Managing Migration Status
- Access Policies - Managing rules for automatic permissioning
Script Backend
Responsible for recording and editing stored scripts. It's not an extensible backend. It supports Python as scripting language, and tasks / operations are realized by the executor module.
Task Backend
Responsible by managing tasks to be executed by the executor module. It's a non-extensible backend.
Ticketing Backend
Responsible for integrating ITSM / Ticketing / Support systems. It's not extensible.
The UI
Main Modules
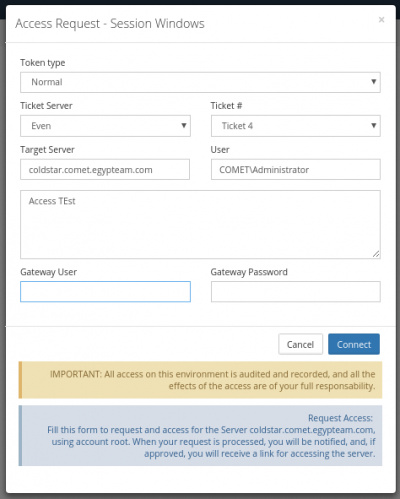
Access
Vault
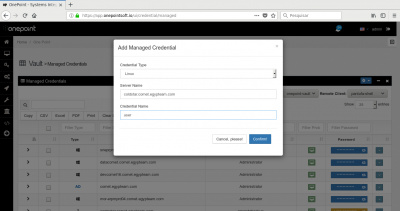
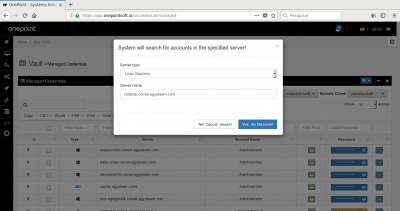
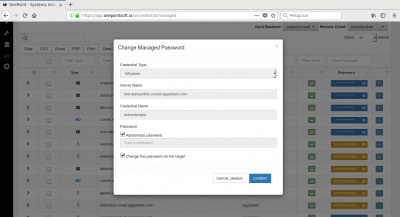
Managed Credentials
My Credentials
Credentials Lists
Delegate Credentials
Task
Apps
Settings
Policies
Development
Scripts
Development Studio
Documents
Videos
Check the Videos page.